The Value is Real.
The Risk Doesn't Have to Be.
Only a zero‑PHI secure data fabric solves both.
-
Eliminates the vulnerability
-
Unleashes the value of authentic health data to securely drive value for unlimited use cases

We don’t prevent breaches.
We make them irrelevant.
Security is foundational.
Elev8Secure strips all 18 HIPAA-defined identifiers – PHI/PII – from data in use, data in motion, and AI training data while preserving authentic valuable data at the individual patient level.

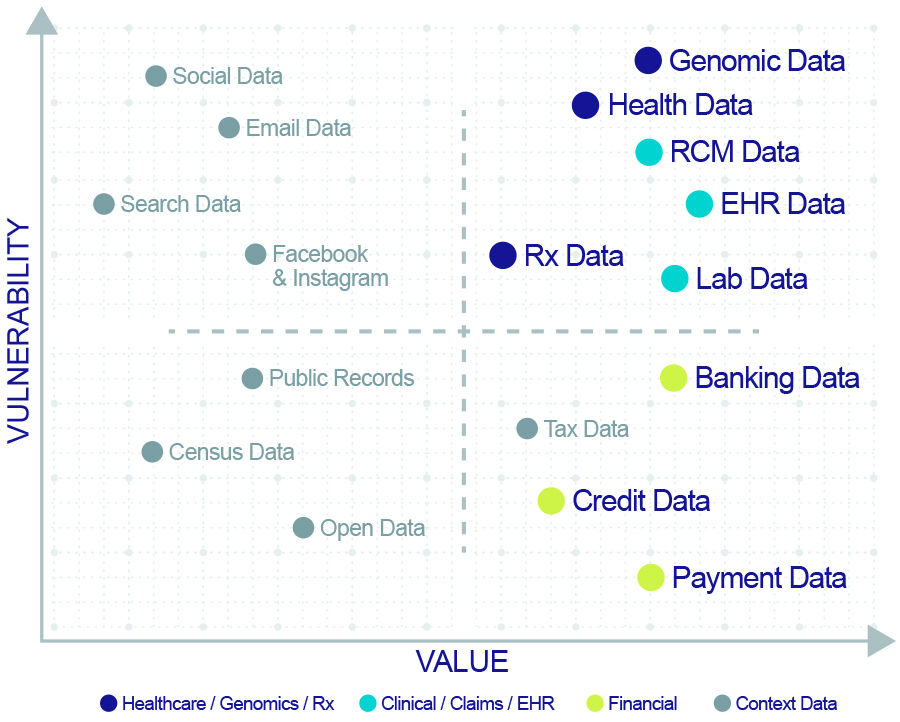
PHI is vulnerable because encryption is insufficient and security standards are deficient.
The Value is Real. The Risk Doesn't Have to Be.
Only a zero‑PHI secure data fabric solves both.
-
Eliminates the vulnerability
-
Unleashes the value of authentic health data to securely drive value for unlimited use cases

We don’t prevent breaches. We make them irrelevant.
Security is foundational.
Elev8Secure strips all 18 HIPAA-defined identifiers – PHI/PII – from data in use, data in motion, and AI training data while preserving authentic valuable data at the individual patient level.
Imagine Where You Can Take Your PHI-free Data
Seamless Data Sharing
Any care, any device, anywhere – with full data sovereignty and consent and control of healthcare data sharing
Secure EHR Workflows Globally
Protect data sovereignty, use any AI anywhere, re-identify protected data on demand
Medical Moonshots
Population health, SDoH, health equity, cancer moonshots, drug discovery, precision medicine, and more
Revenue Cycle Management
Eliminate PHI in transit from clearinghouse to payor to provider
Elev8Marketplace
Monetize your data assets. Contribute to and benefit from the highest-quality health data exchange
How We Strip PHI and Preserve the Value of Authentic Health Data
Breaches happen. Bad actors get inside. Elev8Secure makes it irrelevant.
Even if an attacker gets in, the underlying PHI has been Tokenized, Masked or Redacted by Elev8Secure. What they exfiltrate is worthless – the breach still happens, but the data can't be exploited.
Bad Actors See:
They NEVER See:
TOKENIZE
PHI needed for re-identification is replaced with cryptographic tokens. No replay value to attackers.
8x77fe43zz q8r37dcv49
Sally Smith
MASK
Clinically meaningful data preserved; personal identifiers obscured.
** / ** / 1982
03/06/1982
REDACT
High-value attacker targets with zero clinical value are eliminated entirely.
[ blank field ]
987-00-9876
Bad actors get nothing of value in a breach. Clinicians, researchers, and AI models get PHI-free data.
Field-level surgical precision. Data Owners strip only what must go – all 18 HIPAA-defined identifiers – while preserving the authentic, individual patient data for value creation. Re-identification rights belong exclusively to the data owner, accessed according to their explicit roles and permission.
Configured for the unique needs of each use case.
The result: ZERO PHI exposure.
Zero HIPAA reporting obligation.
-
No cascading financial impacts.
-
No reputational damage.
-
No patients’ identity harm from exposed records.
Finally, unleash the value in the data you own!
The result: Unprecedented opportunities to leverage your data.
-
For superior patient outcomes at lower cost of care
-
Empowering clinicians, researchers, and operational teams with authentic data
-
Leverage data sharing across clinical paths and business processes
Why Authentic Patient Data Matters
The Market Settled for Workarounds. You Don't Have To.
Re-identifiable
Patient/data linkage is preserved and can be restored by the data owner to match real patients to new treatments, unlike anonymization.
Value Preserving
Data integrity is maintained to support longitudinal records that track and manage real patient journeys across time and providers, unlike traditional de-identification.
Compliant
Ensures alignment with regulatory privacy requirements and makes breaches irrelevant, unlike encryption alone.
Actionable
Genuine health data is available for research, population health, and AI-driven insights, unlike synthetic, statistically approximated patient data that can introduce distortions, phantom comorbidities, and bias.
Built for Your Environment
Cloud native, available on AWS, OCI & in hybrid and on-prem environments
Live in other cloud environments in under two weeks
SOC2, HITRUST and HIPAA compliant
21st Century Cures Act compliant
Compatible with all databases
